Hardware crypto wallet provider Trezor has responded after a hacker detailed how he managed to recover his digital assets after losing the PIN to the storage device.
In a detailed YouTube video, Dan Reich, an electrical engineer, explained how he managed to crack a Trezor One hardware wallet containing more than $2 million worth of cryptocurrency.
The wallet owner had spent $50,000 worth of Bitcoin on Theta (THETA) tokens in 2018. The tokens were held on a China-based exchange. The cryptocurrencies were transferred to the hardware wallet following the digital currency crackdown in China; however, he forgot the PIN.
The wallet was automatically wiped after 16 incorrect PIN guesses. The need to recover the assets emerged last year after Theta tokens surged to an all-time high value of almost $15 in 2021. The token has since corrected to trade at $2.7 by press time.
Reich managed to hack the wallet alongside Joe Grand, a hacker who detailed how he explored a potential shortcoming in the storage device.
How the hack was achieved
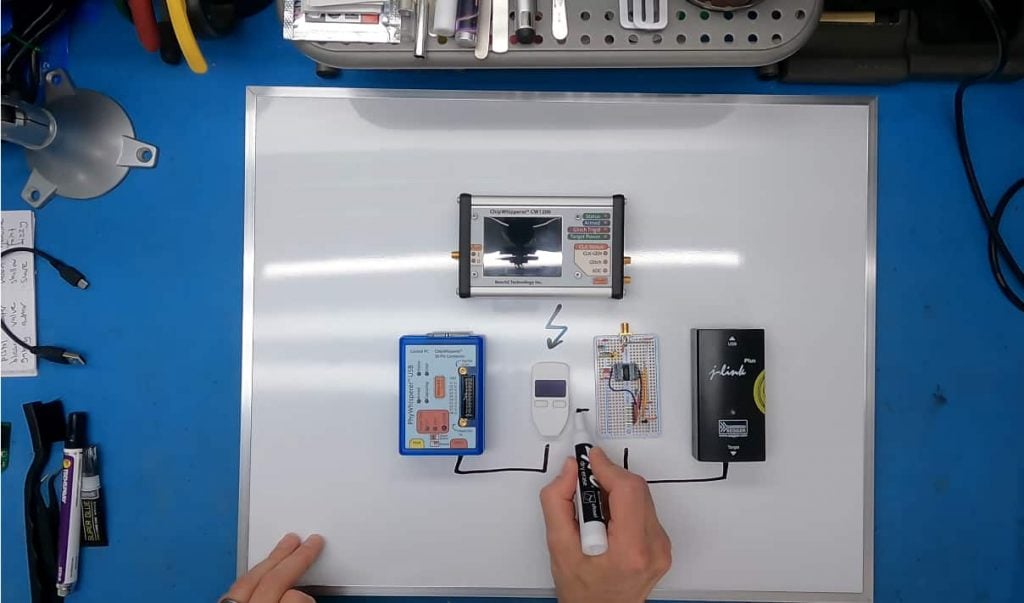
According to Grand, Trezor One wallet temporarily moved the PIN and key to the RAM during a firmware update. At this point, they deployed a tactic identified as a fault injection attack to recover the credentials. Grand stated that the wallet moved the necessary information back to flash after the update.
The technique changed the voltage directed towards the chip. He explained how they managed to get the phrase code and the PIN.
“We are basically causing misbehavior on the silicon chip inside the device in order to defeat security. And what ended up happening is that I was sitting here watching the computer screen and saw that I was able to defeat the security, the private information, the recovery seed, and the pin that I was going after popped up on the screen,” said Grand.
He noted that based on the version of firmware running the wallet, the information was not moved but copied to the RAM. Consequently, if the hack failed RAM could have erased the PIN details and the credentials could be stored in a flash.
The trick enabled them to surpass the security, but the microcontrollers prevented hackers from reading RAM. The hack was also successful considering previous research and guide on how to successfully unlock a Trezor wallet.
They explored a vulnerability that allowed them to put the wallet in firmware update mode enabling Grand to install unauthorized code on the device. This approach helped him to read the PIN and key while in RAM.
Trezor’s response
In response, Trezor indicated that the exploit had been fixed. The wallets can no longer copy or move the key and PIN into RAM. In a YouTube comments section, Trezor expressed:
“Hi, we just want to add that this is an outdated exploit that is not a concern for current users and that we fixed in 2017 right after a report that we received through our responsible disclosure program. This attack requires full physical access to the device, and there is no record of any funds being compromised.”
Watch the full video: How I hacked a hardware crypto wallet and recovered $2 million